One thing holds true in DevOps; abstraction is messy.
Abstraction is something that should make engineers' lives easier, but it can cause a massive amount of confusion and wasted time putting out fires.
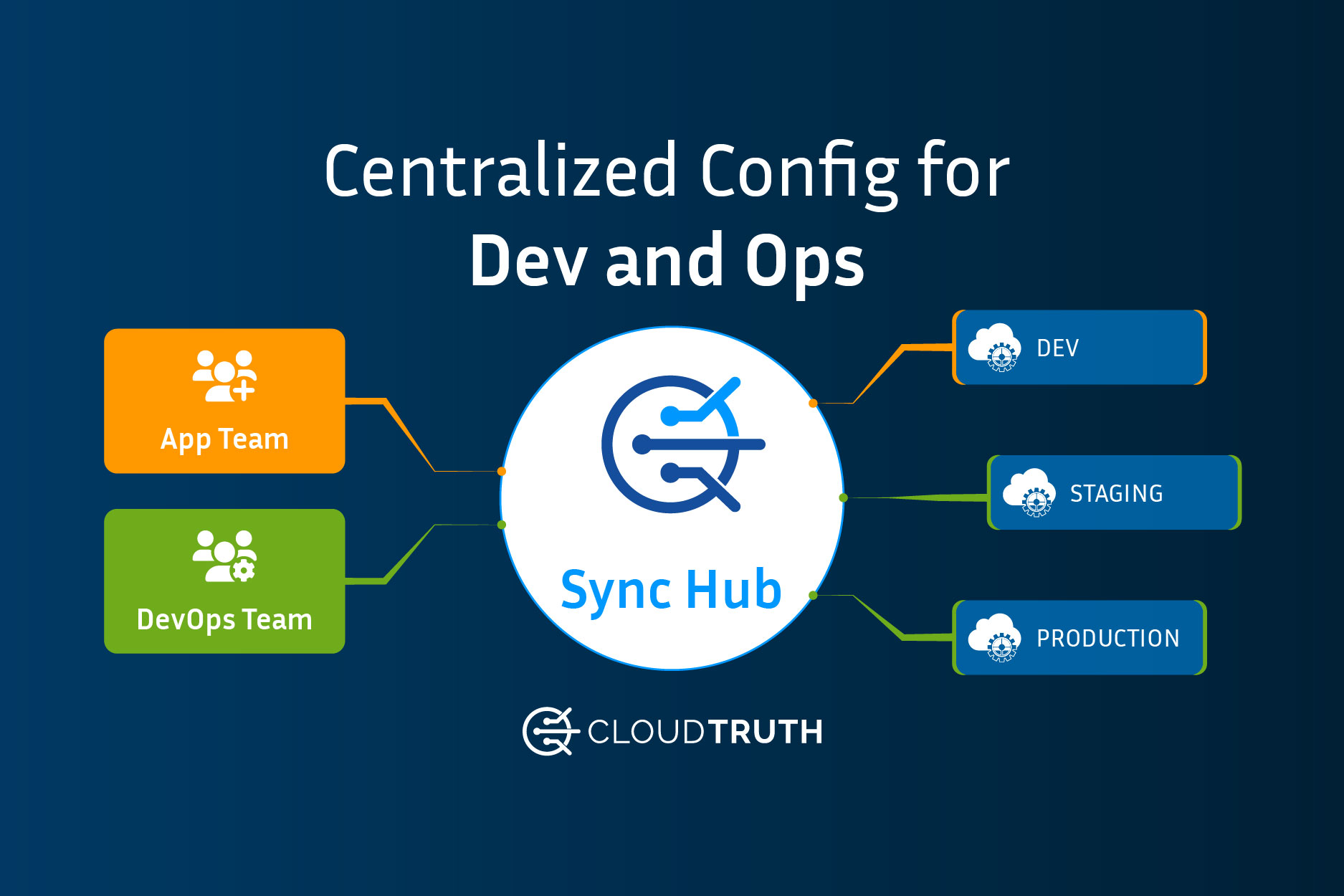
Because configurations are sprawled all over the place due to (one of the contributing factors) abstractions, multi-cloud, hybrid-cloud, and on-prem environments, teams need a place to centrally reference all configurations and templates. This type of approach should integrate with popular parameter and secret stores, pipeline tools and IaC platforms.
That solution is CloudTruth, which decouples the management of configuration data from how the data is consumed.
Pre-Existing Edge
CloudTruth has many popular integrations, including AWS, Azure, GitHub, Argo CD, Jenkins, and Kubernetes (more coming very soon).
Data can be pulled from, for example, AWS SSM. Once the data is pulled, it can be used across any environment. Kubernetes configurations could pull data from CloudTruth that exists inside of AWS SSM. That way, you have one location to manage all configuration data.
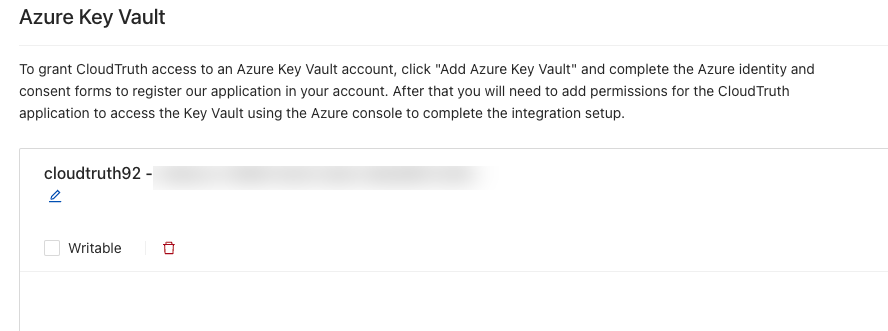
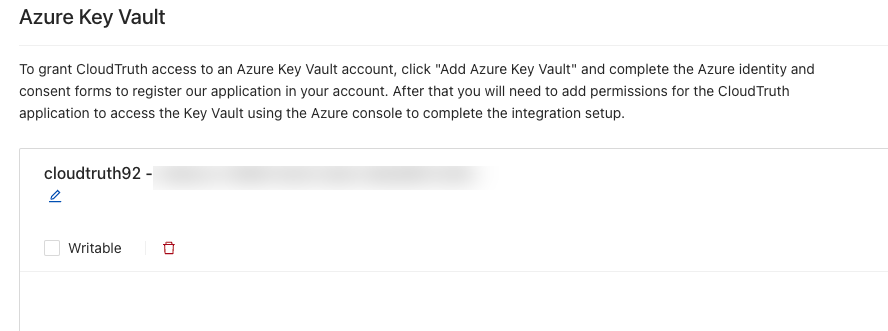
All secrets from Azure Key Vault can be pulled via CloudTruth and sent securely to any of your environments. AppDev teams can store secure information inside of Azure Key Vault and use it across the templates managed by CloudTruth.
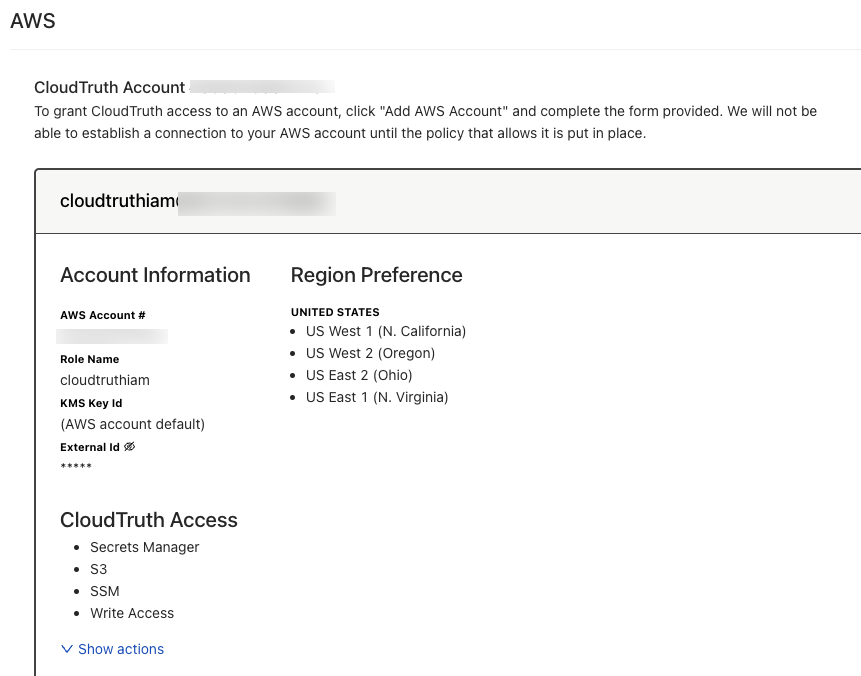
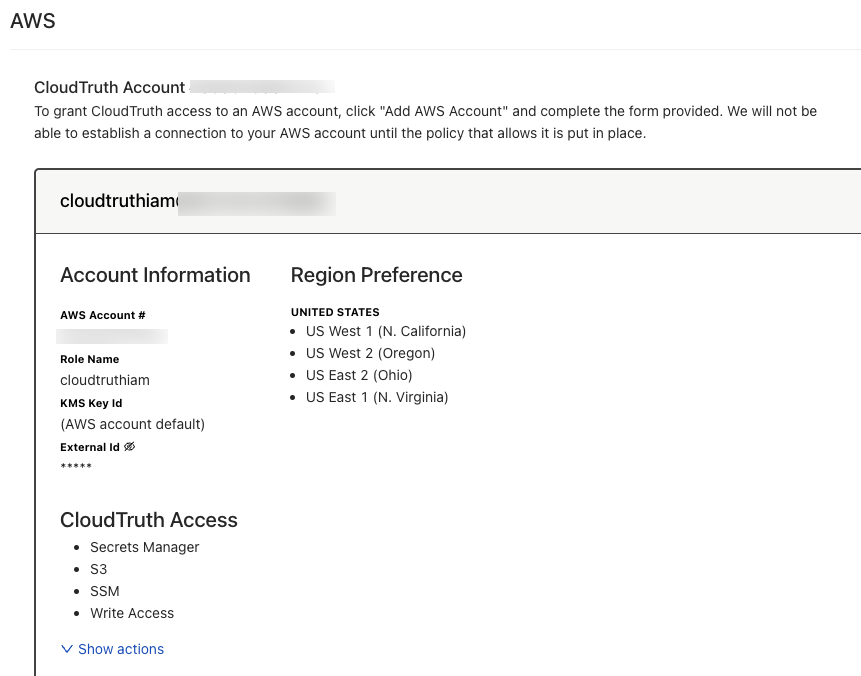
Using the AWS integration, you have the ability to use:
- Secrets Manager
- S3
- SSM
- Write Access
For example, AppDev and DevOps teams may have a Terraform TFSTATE that you want to store inside of S3 for a backend configuration, but perhaps you want it as a template so it can be used outside of S3. The TFSTATE can be pulled from S3 and utilized in Terraform.
Deliver Integrations To The Edge
Thinking about Terraform and Kubernetes clusters, you need a way to deploy. Typically, you'll use a CICD platform to deploy infrastructure and cloud systems. Maybe you're writing Terraform code with several variables and parameters that are needed to be passed in when creating a Kubernetes cluster.
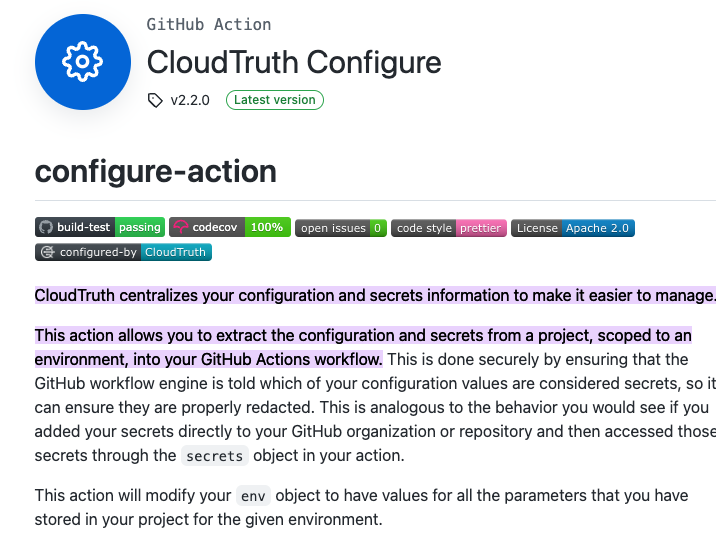
With CloudTruth, you have full integration to any CICD system. That way, you can pass in any value at runtime and ensure that you have one central location for storing all of the configuration data for your CICD pipeline.
With CloudTruth, managing multiple places with plain-text configurations and secrets is no longer a hassle.
AppDev teams can use the edge integrations to pass in Dockerfiles and other containerized apps they want to build. DevOps can also pass in variables and parameters for Terraform code. All in the same location with CloudTruth.
Managing Centralized Configurations
As you saw above, CloudTruth gives you a true, centralized configuration hub that can store parameters, variables, secrets, templates, and integrations across any environment.
Before CloudTruth, most of these configurations were across systems. For example, you might have had your Kubernetes Secrets in the k8s cluster or in something like Vault. Then, you'd have your values.yaml file or other environment variable file for Helm Charts/Kubernetes Manifests in a source control repo. To build the systems, like the Kubernetes cluster, you'd have more variables for your Terraform code throughout another source control repo. Configuration sprawl for many organizations is a huge fire everyone is trying to extinguish.
With CloudTruth, you don't have to worry about any of that. For the first time, you'll have one central location for referencing every piece of configuration data, both plain-text and secret, in one location.
Audit and Logging
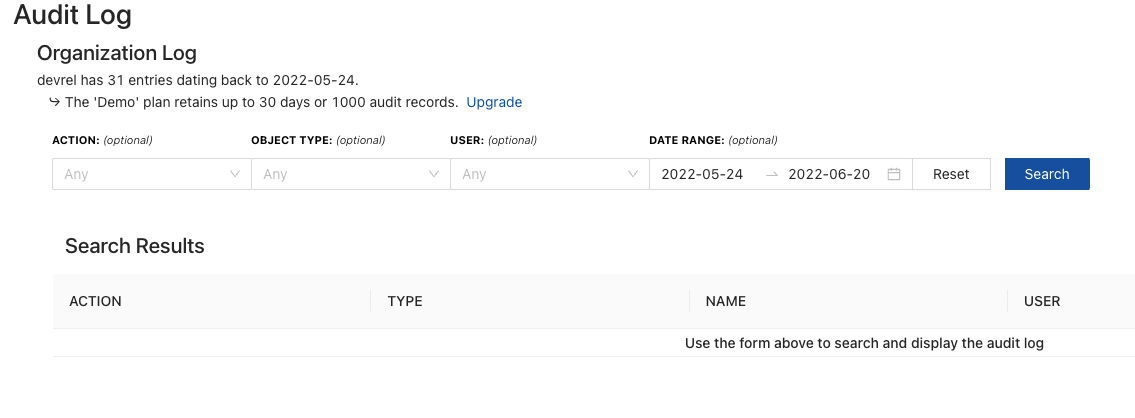
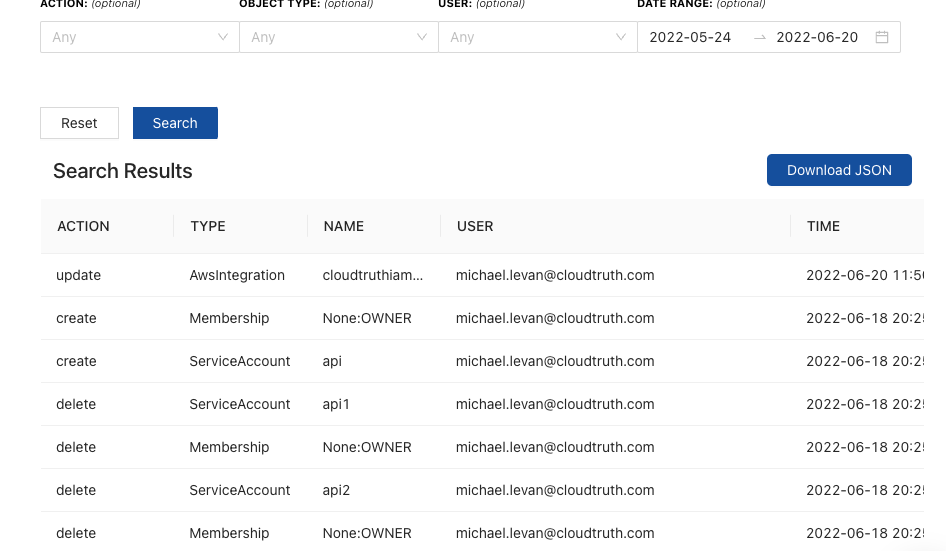
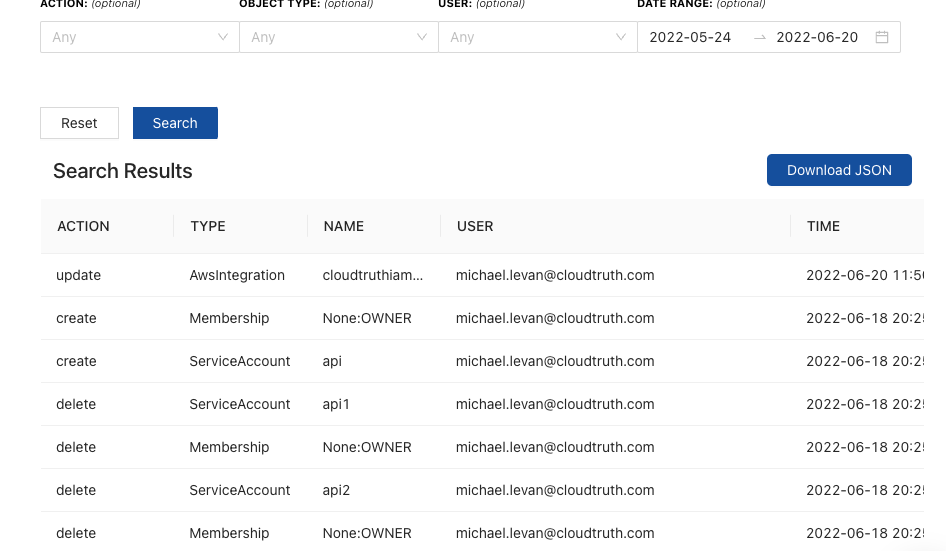
In CloudTruth, you can use the Audit Log to confirm what's happening on the edge and for pre-existing edge cases.
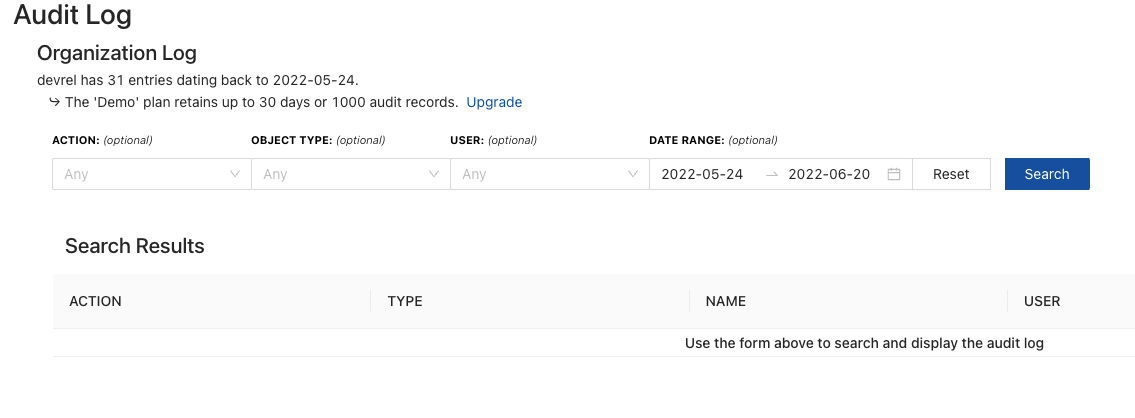
The Audit Log will showcase specific actions, object types, users, and date ranges. This will allow you to understand what configuration data is being passed to a component to ensure compliance.
For example, you can see what API keys are being used to access, retrieve, and create configurations. If something is compromised, you'll be able to see right away.
Getting Started
If you’d like to get started with CloudTruth today, there is a free forever version here. You can also check out some of the latest CloudTruth videos to get going.
Our bite-sized newsletter with DevSecOps industry tips and security alerts to increase pipeline velocity and system security.